Wi-Fi Protocol and Network: A Comprehensive Guide for Network Engineers, Researchers, and Students

5 out of 5
| Language | : | English |
| File size | : | 7687 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 332 pages |
Wi-Fi is a popular wireless networking technology that allows devices to connect to the internet and each other without the need for cables. It is used in a wide range of applications, from home and office networks to public hotspots and industrial settings.
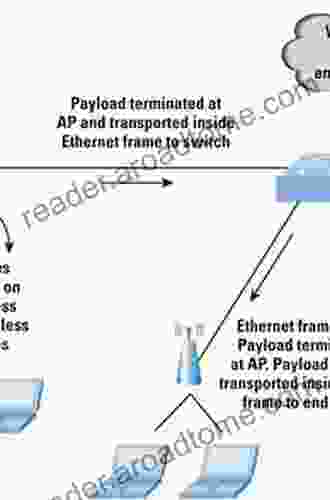
Wi-Fi networks are based on the IEEE 802.11 family of standards. These standards define the physical layer and MAC layer protocols that are used to transmit data over Wi-Fi networks.
Physical Layer
The physical layer of a Wi-Fi network is responsible for transmitting and receiving data over the air. It operates on the 2.4 GHz and 5 GHz frequency bands and uses a variety of modulation and coding schemes to achieve different data rates.
The physical layer is also responsible for managing the contention for access to the wireless medium. This is done using a variety of mechanisms, such as carrier sense multiple access with collision avoidance (CSMA/CA) and time division multiple access (TDMA).
MAC Layer
The MAC layer of a Wi-Fi network is responsible for managing the flow of data between devices. It provides services such as address resolution, data framing, and error control.
The MAC layer also implements the security features of Wi-Fi networks, such as Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA).
Wi-Fi Networks
Wi-Fi networks can be configured in a variety of ways to meet the needs of different applications. The most common types of Wi-Fi networks are:
* Infrastructure networks: These networks use a central access point to connect devices to the internet. * Ad hoc networks: These networks are created directly between devices without the need for an access point. * Mesh networks: These networks use multiple access points to create a more robust and reliable connection.
Wi-Fi Security
Wi-Fi networks are vulnerable to a variety of security threats, such as:
* Eavesdropping: This is the unauthorized interception of data transmitted over a Wi-Fi network. * Man-in-the-middle attacks: This is a type of attack in which an attacker intercepts data transmitted between two devices and impersonates one of the devices to gain access to sensitive information. * Denial of service attacks: This is a type of attack in which an attacker floods a Wi-Fi network with traffic, causing it to become unavailable to legitimate users.
There are a number of steps that can be taken to improve the security of Wi-Fi networks, such as:
* Using strong passwords * Enabling encryption * Implementing firewalls * Using intrusion detection systems
Wi-Fi Applications
Wi-Fi is used in a wide range of applications, including:
* Home and office networks: Wi-Fi is the most popular technology for connecting devices to the internet in homes and offices. * Public hotspots: Wi-Fi hotspots are available in public places such as airports, coffee shops, and libraries. * Industrial settings: Wi-Fi is used in industrial settings to connect devices such as robots and sensors to the internet.
Wi-Fi is a powerful wireless networking technology that has revolutionized the way we connect to the internet. It is used in a wide range of applications, from home and office networks to public hotspots and industrial settings.
Wi-Fi Protocol and Network provides a comprehensive overview of the principles and protocols of Wi-Fi networks, covering both the physical and MAC layers. This book is an invaluable resource for network engineers, researchers, and students looking to gain a deep understanding of the inner workings of Wi-Fi networks.
5 out of 5
| Language | : | English |
| File size | : | 7687 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 332 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!

 Darnell MitchellThe Essential Guide To Delicious Recipes And Meal Plan To Maintain Wellness
Darnell MitchellThe Essential Guide To Delicious Recipes And Meal Plan To Maintain Wellness Ted SimmonsFollow ·17k
Ted SimmonsFollow ·17k Hugh BellFollow ·13.4k
Hugh BellFollow ·13.4k Jerome PowellFollow ·10.2k
Jerome PowellFollow ·10.2k August HayesFollow ·17k
August HayesFollow ·17k Louis HayesFollow ·12.1k
Louis HayesFollow ·12.1k Roberto BolañoFollow ·18.9k
Roberto BolañoFollow ·18.9k Jaden CoxFollow ·3.9k
Jaden CoxFollow ·3.9k Eric NelsonFollow ·9.1k
Eric NelsonFollow ·9.1k
 Brady Mitchell
Brady MitchellUnveiling the Apprehended Vital Truth for the Bride of...
In the tapestry of life, where trials and...
 Eric Nelson
Eric NelsonDivine Energy Harmony Way: Embracing the Power Within for...
In the realm of personal...
 Robert Louis Stevenson
Robert Louis StevensonUnlock the Secrets of Calf Growth and Development: A...
Are you an aspiring...
 Gerald Parker
Gerald ParkerPhysician Life In The Shadow Of Polio: A Harrowing and...
A Riveting Tale of Determination Amidst a...
5 out of 5
| Language | : | English |
| File size | : | 7687 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 332 pages |